Cyberoce's QR code access control features advanced surge protection with multi-layer design, ensuring reliability in harsh environments. It reduces maintenance costs, enhances system stability, and provides integrators with open API support, long-term compatibility, and full technical assistance for smarter, more durable access solutions.
1、 True surge protection: derived from full chain risk prediction and refined design
2、 Stable cornerstone: The core value that surge protection brings to your business
3、 Beyond Hardware: Powerful Soft Power and Support System Empowering integrators
Text:
For system integrators and software platform companies that focus on providing stable solutions, it is very important for hardware to maintain reliable performance for a long time in harsh environments. If access control does not have substantial surge protection, it is easy to encounter problems in outdoor engineering situations such as lightning strikes, unstable power grids, impact caused by inductive loads such as electric locks, and long-term coupling interference. This increases your maintenance costs and damages customer reputation. This is not something that the product's functions can cover, but rather the engineering foundation that determines whether the entire project can succeed and maintain the confidence of end users.

1、 True surge protection: derived from full chain risk prediction and refined design
Our research started with the full chain risk estimation of engineering sites. We understand the real dangers of lightning induction and load conversion, and deeply integrate surge protection into the hardware of QR code access control. Its professionalism is reflected in the graded and collaborative protection system.
Power supply and port graded protection, high-speed TVS diodes are used for nanosecond level precise clamping at the power input end to protect the heart circuit of the rear stage. On these communication ports of the network port, a graded discharge strategy of "gas discharge tube+TVS" is carefully planned. The gas discharge tube acts first to quickly release huge surge energy, and the TVS performs fine voltage cutoff. The two work together to form a line of defense, which can simultaneously resist differential and common mode interference. The preventive design concept, which starts from the source and implements protection along the signal and power paths, is precisely the specific manifestation of the so-called "preventive design concept" of experienced teams. That is to say, our QR code access control has already undergone equivalent standard tests such as IEC 61000-4-5 before leaving the warehouse. We are not only creating products, but also clearing the trouble for you in advance to ensure that the equipment used can work smoothly even if it encounters unexpected electrical pressure, thereby minimizing the problems that may occur on your site.
2、 Stable cornerstone: The core value that surge protection brings to your business
Our powerful surge protection capability in QR code access control adds a bottle of reassurance to your system solution, turning it into tangible economic benefits.
From installation and debugging to long-term maintenance in the later stage, the powerful protective functions equipped internally greatly reduce the probability of sudden failures caused by external environment, equipment being returned for repair, and sudden on-site services, thereby directly optimizing the project's profit margin and improving customer satisfaction.
Delivering equipment that can withstand harsh environmental tests greatly improves the overall reliability and reputation of the system. This provides strong technical support and differentiation advantages for customers with outdoor engineering, factory projects, or complex building projects. The equipment itself has good environmental adaptability and robustness, reducing the need for additional external protective devices and making line layout considerations simpler, thereby achieving faster installation speed and easier maintenance in the future.
3、 Beyond Hardware: Powerful Soft Power and Support System Empowering integrators
We are a long-term access control manufacturing enterprise rooted in this industry. We know that good products must be matched with good services to maximize customer value. What we provide to our customers is not the hardware itself, but a comprehensive support.
Being a original manufacturer has the ability to respond quickly, provide technical support and stable order delivery time, help you flexibly respond to project needs, and seize the leading position in the market.
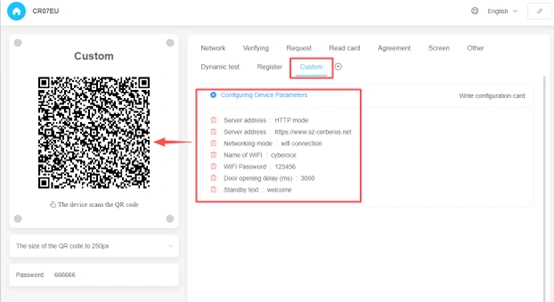
We provide clear and unified standard open protocols (API/SDK), as well as sample code in multiple languages. This set of interfaces has been tested by thousands of integrators worldwide for various projects. Your development team can integrate without any obstacles, and there will be one-on-one technical professional engineers to provide full service. We have strict quality control, and all products leaving the factory must undergo long-term aging testing. We have always adhered to the principle of backward compatibility in product updates, so that your software investment and deployed things can benefit for a long time, seamlessly upgrade, and protect your hard work and customer assets.
Conclusion
In the field of intelligent entrance and exit management, the reliability is the key to gaining trust. Strong surge protection cannot be summarized by a simple slogan. This represents the internal structural quality contained in QR code access control products, the degree of in-depth research and thinking, and the responsible attitude towards partners. It symbolizes our understanding, prevention, and overcoming of engineering risks in the real world. We warmly welcome all system integrators and software platform vendors who are committed to creating top-level access control solutions to learn about the engineering concepts and complete support plans behind our products! Take immediate action and contact us! As a professional manufacturer of access control systems, we offer special privileges to new partners by providing a complete set of development docking agreements, technical materials, SDK toolkits, etc. for free. We are willing to become a trusted technical support force and work together to promote more stable, reliable, and competitive solutions for access control using QR codes to the global market.
#Accesscontrol #QRcodeaccess #doorcontrolsystems #coworkingspace #tearoomspace #etickectcheckingcontrol #QRcodeaccesscontrol #accesssystem #Cerberus #dooraccess #QRcodelock #accessdoor #accesscontrolsystem